Our media regularly draw attention to various Internet threats – mostly at the initiative of the National Security Authority, which monitors and detects possible dangers and informs the public about them. However, these messages are pointless if the audience doesn’t understand them.
That’s why we’ve included a short glossary of terms associated with online security in our blog. Similarly to the rules, we believe that an experienced IT person understands them, but this may not apply to their less web-savvy acquaintances. Do you have one of those as well? Share, educate and save their data!

Antivirus
Software, a program that protects your computer from malicious codes and possible attacks.
Adware
Abbreviation for advertising-supported software. Malicious software (program), displaying ads. When browsing the Internet, it allows pop-ups and sets different websites as your homepage (the first you see when you open your browser). It can be blocked by an antivirus or by a special program – adblocker.
Bot
A computer program that performs automatic tasks on the Internet by itself, e.g. communicates with customers (in this case, it’s a so-called Chatbot and it can be very useful). A bot can be misused to spread messages on social networks, to attack internet services or increase the number of reactions (likes) to a specific post. Multiple interconnected bots form a botnet.
DoS and DDoS attack
Abbreviation for (distributed) denial of service attack. Overloading of a system, usually a website, with a large number of requests from one or more (distributed) sources, which causes its disabling.
Exploit
A program or a specially designed code that exploits vulnerabilities in a system, program or application and causes unwanted behavior – controls them instead of the user, etc.
Hacking
A long-term and purposeful activity in which an attacker (hacker) searches for vulnerabilities in the selected system and tries to use them. It can be used positively (in this case, the so-called ethical hackers search for errors in the system by hacking and they inform authorized people about them so that they can remove them) or negatively (hacker tries to exploit the errors found in the system to steal data, finances, take down the system, etc.).
Hoax
Online spread fake news or deliberate deception. It mostly has three typical features: urgency, reference to an authority (e.g. police source, non-existent scientific studies, etc.) and a request for sharing it further. It’s frequently intended to induce panic or fear.
Injection attacks
Attacks on devices and programs where a malicious code is inserted (injected) in them and it changes the behavior of the program or supplements its function, for example by sending a user’s personal data to the hacker.
Keylogger
A program that tracks what keys a user presses and sends the information to an attacker. This allows usernames, passwords and personal information to be recorded.
Cryptocurrency
Digital money that uses cryptography (various security encryptions, etc.) to secure payments, to control the creation of additional currencies and to verify their transfers. A popular example of cryptocurrency is Bitcoin.
Malware
Abbreviation for malicious software. Any code designed to attack a device and make unwanted changes to it, to reduce its functionality or to completely shut it down.
Phishing
A form of attack in which a hacker poses as a trusted person or institution in order to manipulate and obtain sensitive information from a victim. For example, it could be a fake e-mail from your bank asking you to log in through an attacker’s website or a fake message with a link to enter your credit card details for automatic payment, where your credit card details are saved, allowing the attacker to withdraw money.
Rootkit
Malware that provides privileged access (top root privileges) to your computer.
Skimming
The type of an ATM and payment terminal fraud that uses a device (skimmer) or malware to steal information from a magnetic stripe of a credit or debit card.
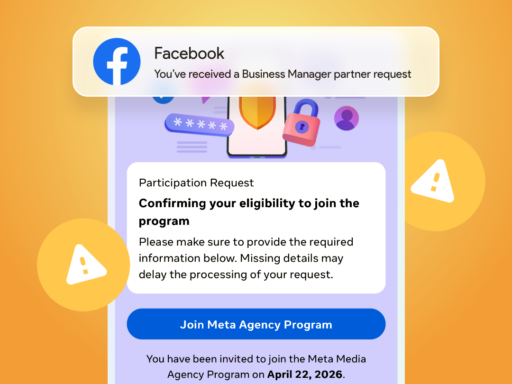
Spoofing
An attack that falsifies transmitted data. For example, it may be a fake e-mail message in which the sender deliberately changes parts of the e-mail so that their author looks like someone else – most often the sender’s name is masked (it appears as an official e-mail of a bank, authority, etc.).
Trojan Horse
A type of malware that appears to be harmless software to persuade the user to install it. Once installed, it performs malicious actions in the background.
Virus
A set of computer instructions (codes) intended to be inserted into another computer program so that it can subsequently replicate. A subclass of viruses are the so-called Worms that can replicate from one computer to another automatically, without human intervention.
XSS Attack
Inserting and functioning of a malicious code, a script that is activated in a specific situation – for example, when logging into a bank application, it sends the login details not only to the bank, but also to the hacker. XSS stands for Cross-Site Scripting.

While putting this glossary together, we’ve come across a number of other concepts that aren’t related to security, but are associated with the online world and are commonly used in the media, although the public may not understand them. That’s why we’ve prepared an extended version of the glossary soon available at glossary.bart.sk. So if you want your grandmother to resist Internet trolls, send her there. So that she knows what influencers are and what they post in their feeds. ?
Sources:
bezpecnenanete.eset.com/sk/kyberneticky-slovnik-pojmov/
cybersec.sk/slovnik-kybernetickej-bezpecnosti/
bezpecnyinternet.sk/slovnik
nbu.gov.sk/kyberneticka-bezpecnost/nbac-slovnik-hybridne-hrozby/index.html
blogit.sk/spoofing/
webappsec.org/projects/glossary/