“How do you protect our data?” This is a question online store operators are hearing more and more often – especially when working with wholesalers, ERP providers, or corporate IT departments.
Today’s business partners don’t base their decisions solely on features, speed, or integrations. They also want to know how you manage access rights, backups, disaster recovery, and data protection. Not because they don’t trust you – but because they’re responsible for their own data.
To them, you’re not just a vendor. You’re a part of their system. And if something goes wrong on your side, it can disrupt their operations, affect service reliability, and undermine customer trust.
That’s why these questions are becoming more common – in tenders, contracts, and everyday communication. And it’s expected that you – not just your tech team or external provider – will know how to answer them.
In this article, we’ll walk through four common security-related questions you might face – and how to respond to them clearly and professionally.
1. “How do your backups work?”
Your partners want the peace of mind that their data is safe – even in case of a system outage, cyberattack, or human error.
Just one mistake during a price list import can erase wholesale pricing agreements. Without backups, restoring that data manually could lead to data mismatches, order delays, and loss of credibility.
Regular, reliable backups are a key pillar of secure infrastructure – and increasingly a formal requirement from B2B clients.
Some contracts even include clauses that require suppliers to guarantee regular backups, recovery testing, and historical version storage. If you commit to this, make sure you understand exactly what it entails.
Professional-grade backups include:
- automated, regular backups – ideally daily or more frequently for high-traffic stores,
- off-site storage (e.g. cloud or object storage) to protect against hardware failure or cyberattacks,
- encryption to safeguard sensitive data even in case of a breach,
- regular recovery testing,
- version history for rollbacks,
- point-in-time recovery to restore the database to a specific moment.
If your backup system meets these standards, you can confidently explain that you’re prepared for the unexpected.
2. “Who has access to your system?”
If a partner shares sensitive business data with your eshop – contracts, orders, customer information – they naturally want to understand who can access this data and how that access is secured.
Large enterprises or corporate customers may send you a security questionnaire or an RFI (Request for Information) before signing a contract. This often includes requirements like:
“Describe your access control mechanisms and safeguards against unauthorized access.”
Responsible access management includes:
- unique accounts for each user (no shared “admin” logins),
- role-based permissions – different levels for admin, warehouse, marketing, or support,
- two-factor authentication (2FA) for account protection,
- regular permission reviews – especially during onboarding or offboarding,
- activity logs – to track who accessed or modified what and when.
A well-configured access control system builds trust and shows your partners that you take data stewardship seriously.
3. “What happens if your eshop goes down?”
Outages can happen – what matters is how quickly they’re detected and how effectively you respond. Corporate clients want to know how you’ll handle downtime and how long recovery will take. Contracts increasingly reference terms like RTO (Recovery Time Objective), uptime monitoring, and disaster recovery plans.
A well-prepared eshop should include:
- uptime monitoring with alerts,
- a documented disaster recovery plan with clear responsibilities,
- a defined recovery sequence (e.g. payments, orders, admin),
- access to backups for fast data restoration,
- internal communication that informs your team and clients of progress and timelines.
With these measures in place, you present yourself as a reliable partner who can handle disruptions with confidence.
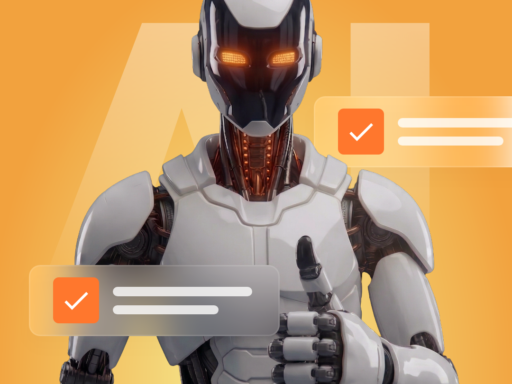
4. “Where is our data stored and how is it protected?”
In public procurement and B2B partnerships, this question is often key. Partners want assurance that their data is securely stored, accessible only by authorized personnel, and compliant with relevant laws – especially GDPR.
Requirements like data residency within the EU and encryption in transit and at rest often appear in contracts and technical documentation.
If you use AI (for product recommendations, chatbots, or dynamic pricing), it’s important to know what data is collected, how it’s processed, and whether it aligns with the AI Act. EU user data should be processed securely, fairly, and preferably stored within the EU.
Secure information management includes:
- encryption during transfer and at rest,
- data storage in trusted data centers – preferably within the EU,
- access controls – knowing exactly who is authorized to view or edit data,
- audit trails – the ability to verify who interacted with the data and when,
- AI data governance – ensuring data usage complies with legal requirements,
- GDPR compliance – including documentation and safeguards for user rights.
If these elements are in place, you can confidently state that your eshop meets modern data protection standards.
Why it matters now
Security is no longer just a technical concern – it’s a measure of your business credibility.
As of October 2024, the European NIS2 directive has come into force, tightening security standards for key sectors such as healthcare, transport, energy, and digital services. While it may not directly affect most online stores, many of your partners and suppliers are already covered – and they must ensure their external systems meet stricter requirements.
If you collaborate with companies from these industries, it’s highly likely that security expectations will soon extend to you too. Being able to confidently answer questions about backups, access, downtime, and data protection gives you a competitive edge – in tenders and in trust-building.
You don’t need to know every technical detail – you just need a solid setup and the ability to explain it clearly. When you’re ready to answer, you show that you’re a reliable partner for any business goal.
B2B E-commerce Security FAQ: What Partners Want to Know
Why do B2B partners ask about backups?
B2B clients often handle sensitive data and want assurance that it won’t be lost due to a system crash or human error. Backup policies are now a standard part of RFPs and contracts. Partners expect you to offer point-in-time recovery — the ability to restore data to a specific moment.
What does professional e-commerce backup look like?
Professional backup means automated daily (or more frequent) backups, secure off-site storage, encryption, regular recovery tests, version history, and the ability to restore your database to a specific time. It builds trust and significantly reduces risk.
What access control policies are expected for B2B stores?
Each user should have their own account with role-based permissions. Two-factor authentication, regular access reviews, and activity logs are also expected. These practices show that your e-commerce system handles partner data responsibly and securely.
What should a disaster recovery plan include?
A solid disaster recovery plan defines who is responsible for what, the order in which systems are restored (e.g. payments, orders, admin), and how you communicate internally and externally during downtime. It should also include uptime monitoring and fast access to backups.
Where should partner data be stored?
Ideally, in encrypted form within data centers located in the EU. This is often a contractual requirement, especially when working with government or enterprise clients. Responsible data storage also means full auditability and strict access controls.
Do AI tools pose a data security risk?
They can. If you’re using AI for product recommendations, pricing, or customer service, it’s crucial to know what data is being processed and ensure compliance with GDPR and the upcoming EU AI Act. Make sure AI tools handle data securely, transparently, and — ideally — within the EU.
What is NIS2, and does it affect online stores?
NIS2 is an EU directive that raises cybersecurity standards for companies in critical sectors. While it may not apply directly to most e-shops, your B2B clients might be affected — and they could require you to meet higher security standards too. Being ready for these demands gives you a competitive edge.